Beyond Patterns: How SnortML and Agentic AI Are Redefining Intrusion Detection
Traditional intrusion detection systems have long relied on signature databases to flag known threats. But as attacks become more sophisticated, security is evolving. Two key innovations—SnortML and Agentic AI—are redefining how sensors think, moving from simple pattern matching to contextual understanding. Below, we answer the most pressing questions about this transformation.
What is the fundamental difference between signature-based detection and machine learning-based detection in intrusion detection systems?
Signature-based detection operates like a wanted poster: it has a fixed list of known threat patterns (signatures) and flags anything that matches exactly. This approach is fast and reliable for known attacks, but it fails against novel or obfuscated threats. Machine learning (ML) detection, in contrast, learns from data what normal and malicious traffic look like without relying on predefined patterns. Instead of asking, "Does this match a known signature?" it asks, "Does this behavior make sense given what I've learned about normal and abnormal activity?" This allows ML models to identify zero-day attacks, polymorphic malware, and subtle anomalies that signatures miss. The shift is from rigid, pattern-based matching to probabilistic, context-aware analysis. SnortML exemplifies this evolution by integrating ML directly into the Snort IDS framework, enabling sensors to adapt to new threats dynamically.
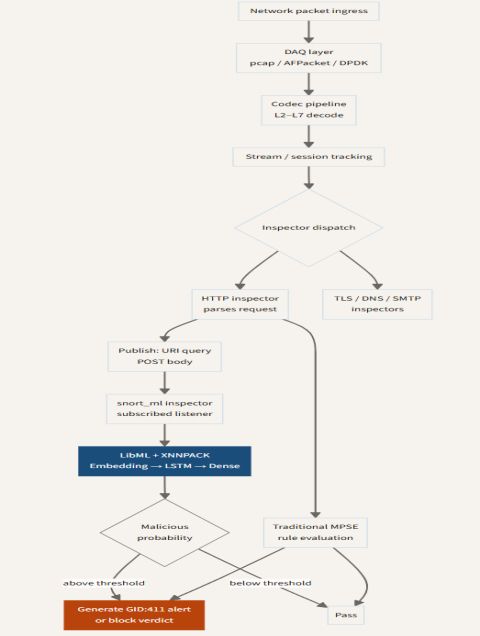
How does SnortML represent a shift in intrusion detection architecture?
SnortML marks a departure from the classic Snort architecture, which relied heavily on rule-based signatures. By embedding machine learning models into the detection pipeline, SnortML allows the sensor to analyze traffic in real time and make decisions based on learned behavioral patterns rather than static rules. This architectural change means the system can update its detection capabilities without manual rule writing, reducing the burden on security analysts. The sensor no longer just matches packets against a list; it "thinks" about each packet's context—time of day, protocol usage, payload characteristics—and assigns a probability of malice. SnortML also supports ensemble methods, combining multiple ML models for higher accuracy. This shift from reactive signature updates to proactive behavioral analysis makes the IDS more resilient against evolving attack techniques and reduces false positives by understanding what "normal" looks like for each network environment.
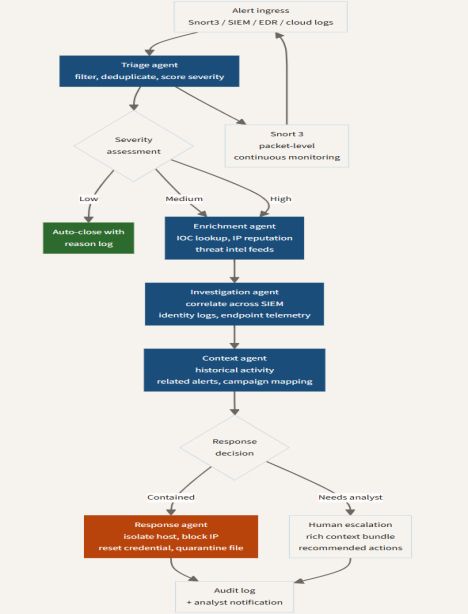
What role do autonomous agents (Agentic AI) play in modern intrusion detection?
Autonomous agents, or Agentic AI, take the contextual reasoning of machine learning a step further. Instead of just flagging suspicious events, these agents can independently investigate, correlate, and even respond to threats in real time. In an IDS context, an agentic AI might notice a subtle anomaly—like a sensor reading that deviates slightly from baseline—and then proactively query other sensors, check authentication logs, or isolate a compromised host without human intervention. This distributed intelligence allows the security system to operate at machine speed, outpacing fast-moving attacks. Agentic AI also learns from each interaction, improving its decision-making over time. The shift is from a passive alert generator to an active, autonomous defender that can adapt its strategies based on the network's current state. When combined with SnortML, these agents can leverage ML-driven insights to make nuanced decisions about whether a behavior is truly malicious or simply unusual but benign.
Why is context important in intrusion detection beyond pattern matching?
Pattern matching treats every packet in isolation, ignoring the broader narrative of network activity. A single DNS query might be benign on its own, but if it comes from a server that previously exhibited cipher mismatches and abnormal TLS stacks, it could indicate command-and-control communication. Context—such as timing, protocol sequencing, user behavior baselines, and sensor correlations—provides the story behind the data. Machine learning models can incorporate these contextual features to reduce false positives (e.g., distinguishing a server update from an exfiltration attempt) and detect attacks that span multiple connections or protocols. For instance, a signature might miss a slow data leak because each individual packet looks normal, but a context-aware model would notice the unusual total data volume over time. This is why the question shifts from "Is this packet known?" to "Does this activity make sense in the current environment?" SnortML and agentic AI excel at capturing and acting on this contextual richness.
How does machine learning enable sensors to "think" rather than simply match patterns?
Machine learning gives sensors the ability to generalize from past experience. A signature-based sensor is like a librarian who only recognizes books by their barcode—if the barcode is new, the book is invisible. An ML-enabled sensor is like a librarian who has read thousands of books and can infer a book's topic from its cover, table of contents, and writing style. Algorithms such as neural networks, decision trees, and clustering can identify underlying structures in network traffic that aren't encapsulated by simple signatures. The sensor learns what "normal" looks like for its own network—modeling traffic patterns, user behaviors, and system calls—and then flags deviations that exceed a learned threshold. This process is continuous; the sensor updates its understanding as new data flows in. It doesn't just ask, "Is this packet on the blacklist?" but rather, "How surprising is this packet given everything I've seen before?" SnortML operationalizes this by training models on historical PCAP data and then deploying them inline to make real-time probabilistic judgments.
What challenges does the shift to AI-driven detection introduce?
While AI-driven detection offers powerful advantages, it also brings new challenges. Machine learning models require large, high-quality datasets for training, which can be difficult to obtain for rare or custom attacks. Models can also produce false positives, especially when the network's behavior changes legitimately (e.g., software updates or new services). Adversarial attacks can fool ML models by crafting traffic that appears benign to the algorithm but is actually malicious. Additionally, the "black box" nature of some deep learning models makes it hard to explain why a sensor flagged a particular event, complicating incident response and compliance. Deployment latency and computational overhead are concerns for real-time interception. Agentic AI compounds these issues by introducing autonomous actions that could have unintended consequences if the model makes an incorrect judgment. Security teams must invest in model monitoring, retraining pipelines, and human oversight to ensure AI-enhanced IDs remain reliable and trustworthy.
What is the future of intrusion detection with agentic AI?
The future of intrusion detection lies in fully autonomous, self-learning security ecosystems where agentic AI orchestrates multiple sensors, each powered by machine learning models like SnortML. These agents will not only detect anomalies but also hypothesize attack chains, simulate responses, and adapt defenses in real time. We can expect integration with threat intelligence feeds so that agents proactively seek out indicators without relying on signatures. Autonomous agents will also collaborate with each other across different network segments, forming a collective intelligence that can spot distributed attacks. The human role will shift from monitoring alerts to high-level strategic oversight and model governance. However, this vision requires breakthroughs in explainability, robustness, and safety to prevent AI from making catastrophic mistakes. Ultimately, the direction is clear: IDS will evolve from a passive signpost to an active, thinking participant in network defense, constantly asking not just "Is this suspicious?" but "What should I do about it?"
Related Discussions