Centralize Your Certificate Lifecycle: How to Orchestrate Public CAs with IBM Vault
Introduction
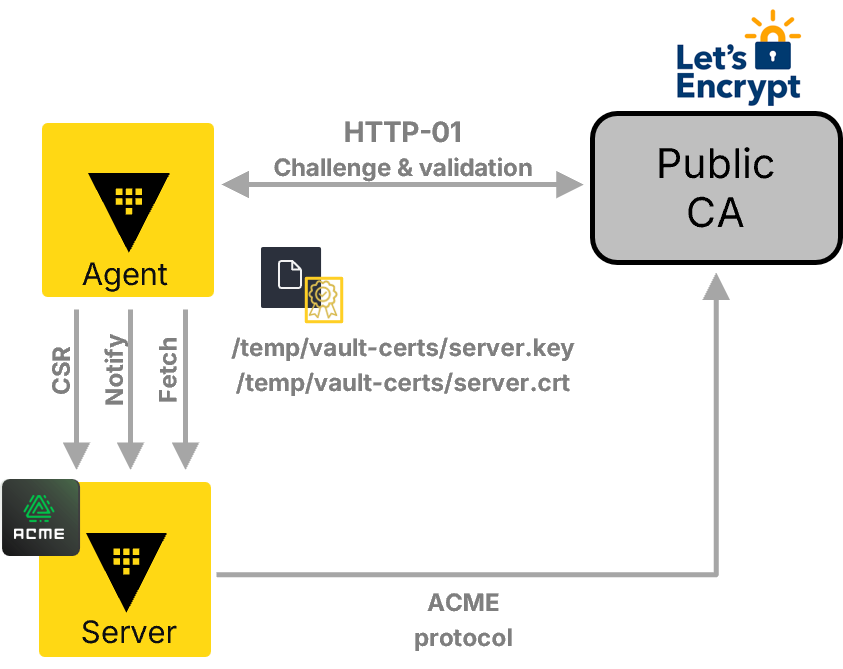
Managing X.509 certificates across an enterprise is often a fragmented, manual process—especially when some certificates must be publicly trusted. You've likely automated internal PKI with HashiCorp (now IBM) Vault, but the moment a service requires a certificate for a customer-facing website, the automation stops. This creates a dual-track management system: one for private certs, another for public ones. The result is operational overhead, missed renewals, and governance silos. With the latest Vault Enterprise expansion, you can now orchestrate public certificate authorities (CAs) directly within Vault, unifying the entire certificate lifecycle under a single pane of glass. This guide walks you through the steps to integrate and orchestrate public CAs, eliminating the trust gap once and for all.
What You Need
Before you begin, ensure you have the following prerequisites:
- IBM Vault Enterprise with the PKI secrets engine enabled (version 1.15+ recommended).
- Access to a public CA that supports the ACME protocol (e.g., Let's Encrypt, DigiCert).
- Administrative privileges on Vault to configure secret backends and policies.
- A Vault token or authentication method with sufficient permissions to read, write, and manage PKI roles.
- Network connectivity from Vault to the public CA's ACME endpoint (outbound HTTPS).
- Domain control validation capability (e.g., DNS or HTTP challenge responder) to prove ownership of domains.
Step-by-Step Guide
Step 1: Enable and Configure the PKI Secrets Engine
First, you need to activate the PKI engine in Vault. This engine will serve as the central hub for both private and public certificate issuance. Run the following command in your Vault CLI or use the API:
vault secrets enable pki
Then, configure a default issuer for internal private PKI (this is optional but recommended for hybrid workflows):
vault write pki/root/generate/internal common_name='your-internal-ca' ttl=87600h
This sets up an internal CA that Vault can manage alongside public CAs. You'll later define separate roles for public certificates.
Step 2: Set Up ACME Provider for Public CA
Vault's public CA integration uses the ACME (Automated Certificate Management Environment) protocol. To connect to a public CA, you must create an ACME provider configuration. Use the pki/acme endpoint:
vault write pki/config/acme directory_url='https://acme-staging-v02.api.letsencrypt.org/directory'
Replace the directory URL with your chosen public CA's ACME endpoint. For production, use https://acme-v02.api.letsencrypt.org/directory or your corporate CA's URL. Vault securely stores the CA's credentials (e.g., account key) once you register later.
Step 3: Define a Role for Public Certificate Issuance
Roles in Vault control the policies for certificate generation. Create a role specifically for public certificates, specifying allowed domains, key types, and TTLs:
vault write pki/roles/public-cert allowed_domains='example.com,*.example.com' allow_subdomains=true max_ttl='90d' key_type='ecdsa' key_bits='256'
This role ensures that only authorized requests for your domains are processed. Adjust the max_ttl according to your public CA's limits (usually 90 days for Let's Encrypt).
Step 4: Register With the Public CA (Domain Validation)
To actually issue certificates, Vault must prove domain ownership. This step requires you to configure a domain validation provider. Vault supports both DNS-01 and HTTP-01 challenges. For DNS-01, you'll need credentials to update your DNS provider (e.g., AWS Route53, Cloudflare). Configure the validation method via the pki/config/issuers endpoint:
vault write pki/config/issuers dns01_provider='route53'
For HTTP-01, Vault temporarily exposes a web endpoint. You'll need to ensure your Vault server is accessible on port 80 from the public internet (not recommended for production; use DNS-01 instead).
Once configured, Vault will automatically complete the ACME challenge when a certificate is requested.
Step 5: Request a Public Certificate via Vault API
Now, any authorized client can request a publicly trusted certificate using the same Vault API they use for private certificates. Use the pki/issue/public-cert endpoint (assuming the role name is public-cert):
vault write -format=json pki/issue/public-cert common_name='www.example.com'
Vault returns the certificate, private key, and issuer chain. The private key is encrypted with your Vault transit key or returned in plaintext depending on your policy. This request triggers the ACME registration and domain validation automatically—no manual steps needed.
Step 6: Automate Renewal and Revocation
To maintain a zero-touch lifecycle, set up Vault's periodic renewal capabilities. Use vault lease renew commands or configure your application to re-request certificates before expiration. Vault can also automatically revoke certificates when they are deleted or when a lease expires. For public CAs, revocation is sent to the CRL (Certificate Revocation List) via ACME.
You can monitor all certificates—both private and public—through Vault's audit logs and the PKI UI, providing a central view of expiration dates across your enterprise.
Tips for Success
- Start with a staging environment: Use Let's Encrypt's staging server (acme-staging) to test your configuration without hitting rate limits.
- Use DNS-based validation whenever possible: It's more secure and doesn't require exposing Vault to public HTTP traffic.
- Enforce unified policies: Create Vault policies that require all public certificate requests to go through a specific role, and audit all actions for compliance (NIST, PCI DSS, SOC2).
- Monitor renewal windows: Even with automation, set alerts for certificates approaching expiration to catch any Vault failures early.
- Leverage Vault's secrets as a service: For microservices, generate short-lived certificates that rotate frequently—public CA integration works seamlessly with this pattern.
- Document your domain ownership methods: If you switch DNS providers or add new domains, update your Vault configuration accordingly.
By following these steps, you eliminate the dual-track management problem and bring all certificate operations under a single, automated workflow. Your teams gain efficiency, your governance becomes consistent, and those dreaded certificate outages become a thing of the past.
Related Discussions